Homograph Attacks

In This Article
• What are homographs?
• How are they used?
• Will my browser protect me?
• What can I do to avoid them?
(No time to read right now? Just want to see the list of things to know? Here you go.)
Homograph attacks are a sneaky way hackers try to fool people with bogus web addresses.
 A homograph, in the real world, is a word that is spelled the same but has different meanings. Examples are “bats” (small mammals or sports equipment) and “wave” (hand greeting or moving water).
A homograph, in the real world, is a word that is spelled the same but has different meanings. Examples are “bats” (small mammals or sports equipment) and “wave” (hand greeting or moving water).
A homograph, on the web, is a domain name (“web address”) that appears to be spelled the same but is actually different due to non-English letter substitutions.
Web Domain Homographs
In a web domain homograph attack, a hacker registers a web address using non-Latin alphabet characters.
For example, by using Cyrillic (Russian language) letters that look like “a” or “o”, a hacker can create a web address that seems to be “apple.com” or “google.com”. But the letters that appear to be an “a” or an “o” are really different letters, and the websites those addresses point to are not Apple or Google.
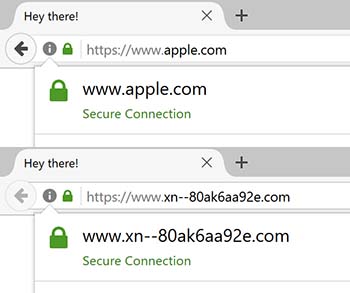 The web address starting with “www.xn––” in the bottom half of the image here will actually be displayed as “www.apple.com” in some browsers, making it indistinguishable from the real one in the top half.
The web address starting with “www.xn––” in the bottom half of the image here will actually be displayed as “www.apple.com” in some browsers, making it indistinguishable from the real one in the top half.
If the hacker uses such a homographic web address in a phishing email, many people may click on the link and get themselves into trouble.
Lazy Hackers
Some lazy hackers don't bother with homograph attacks and simply register web addresses that are merely similar to real ones. For example, they might register faceboook.com or gooogle.com, hoping people will make typos.
Those are not realistic examples, though, because big companies like Facebook and Google usually register as many common typos and other misspellings for their legitimate domains as they can, just to avoid problems. But smaller companies may not do so.
Web Browser Defense
 Can't web browsers detect these differences?
Can't web browsers detect these differences?
Technically they can, and some do, especially the latest versions of the most common browsers. But there are ways hackers can circumvent some of the browser defenses, so you can't just rely on your browser to protect you.
And because hackers can buy inexpensive SSL (security) certificates using the homograph domain names, they can create a website that appears to be a “secure” site to your web browser. So looking for the “padlock” or “https” is no help either.
From Proof of Concept to Real Word Exploit
The homograph attack originally was just a “proof of concept” when one of the Internet's governing bodies opened things up to non-English alphabets.
Since then, unfortunately, it has turned into an actual exploit. Homograph-based websites (even ones using SSL certificates) have been found that mimic financial, eCommerce, technology, and other types of sites.
A leading web security research company that monitors web traffic said that, “Despite the emergence of preventative measures, every day dozens of homograph domain names are accessed” by web users.
Your Defenses 
There are some things you can do to protect yourself from homograph attacks:
Never click links in email or social media posts, even if they look legitimate. It's safer to manually enter the web address into your browser, being careful to spell it correctly.
Always keep your web browser updated to get the latest security patches and new features designed to keep you safe.
Always use two-factor / multi-factor authentication (2FA/MFA), if available, for websites you log into (2FA/MFA is that thing where you have to enter a code texted or emailed to you, in addition to your username and password).
Questions?
If you have any questions about anything here or if there's an issue you'd like us to talk about please get in touch.
Want More Info Like This?
Get our Free Newsletter
